Published: May 11, 2026
In the world of cybercrime, old methods are often the most effective. We are currently seeing the return of a phishing campaign targeting Polish entrepreneurs and domain owners. The criminals are impersonating the hosting giant home.pl, scaring users with claims that their domain is about to expire and that debt collection is on the way.
We analyzed an authentic example of such a message to show you how to recognize the scam in seconds.
What does the trap look like? (Technical analysis)
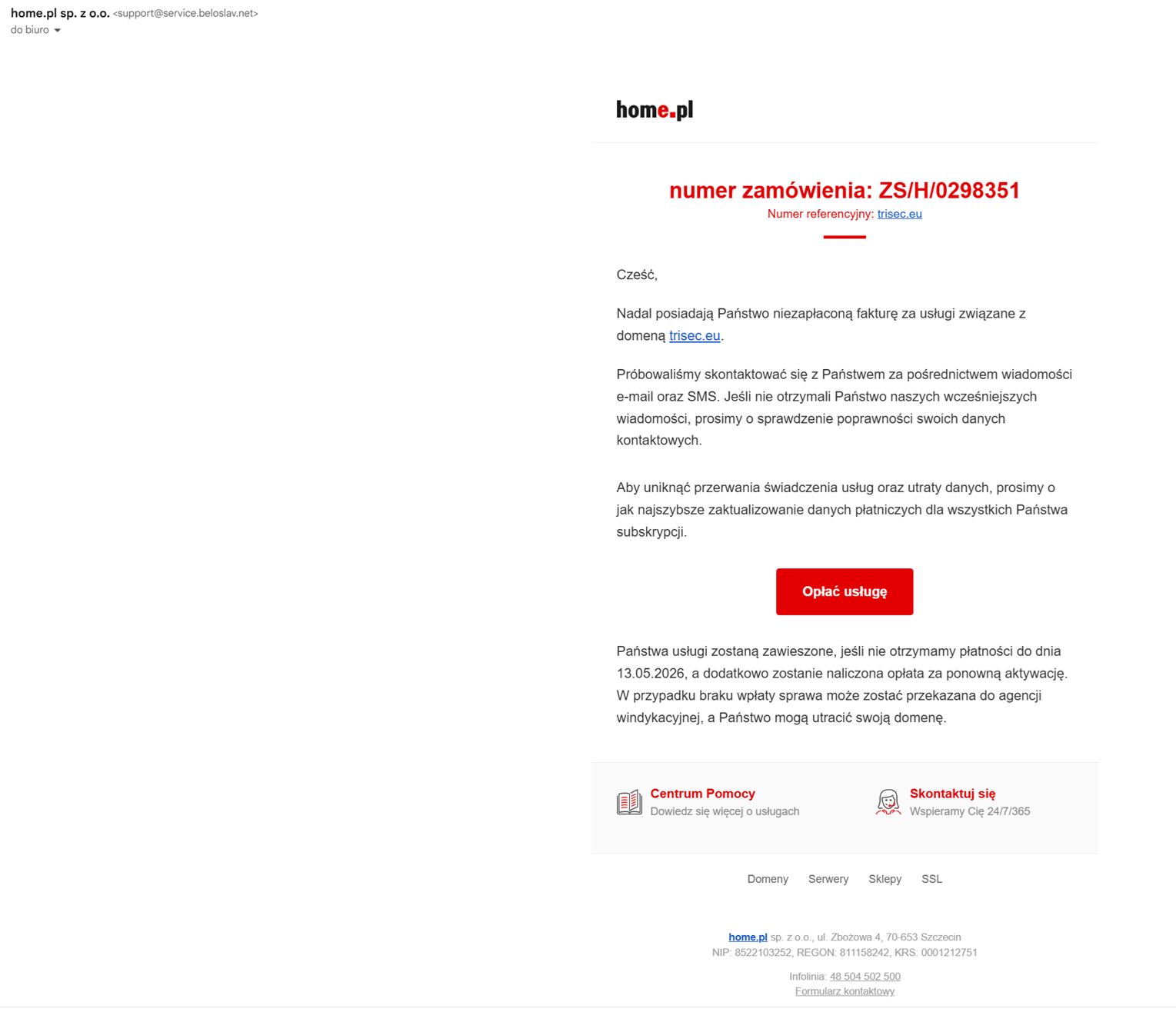
At first glance, the email looks professional: it contains the home.pl logo, the correct address details of the company in Szczecin, and a threatening message about an overdue invoice. The devil, however, is in the details of the message headers.
1. Fake sender
In the "From" field we see: home.pl sp. z o.o. <support@service.beloslav.net>.
beloslav.net domain. This is a private or compromised domain that has nothing to do with the service provider.2. Authentication results (DMARC Fail)
The headers read: dmarc=fail (p=NONE sp=NONE dis=NONE) header.from=beloslav.net.
3. Suspicious payment link
The "Pay for service" button leads to: https://raykyte.com/22672080.
Anatomy of the manipulation: what hooks the victims?
The scammers use proven psychological techniques designed to lull your vigilance:
- Time pressure: "Your services will be suspended if we do not receive payment by 13/05/2026." You are meant to panic and pay without checking the invoices.
- Threat of penalty: mentions of a "reactivation fee" and "transferring the case to a debt collection agency" are designed to instill fear of financial and legal consequences.
- Partial personalization: the email subject line includes the victim's domain name (e.g.
trisec.eu), giving the impression that the message is authentic and addressed specifically to you.
How to defend yourself? 3 golden rules
- Always check the sender's email address. Don't just look at the displayed name (e.g. "home.pl"), but at what is between the angle brackets
< >. If the domain after the@sign is different fromhome.pl, delete the message immediately. - Log in directly. Never pay for services through links sent in an email. Go to the official provider's website (by typing the address manually in your browser) and check the payment status in your client panel.
- Verify links before clicking. Hover the mouse cursor over the button (don't click!) and at the bottom of the browser you will see where the link actually leads.
Remember: no major operator sends payment demands with links to exotic domains likeraykyte.comorbeloslav.net. If you received a similar message — it is an attempted theft. Stay vigilant!
 Consulting sp. z o.o.
Consulting sp. z o.o.